Comprehensive Security Testing for Decentralized Applications
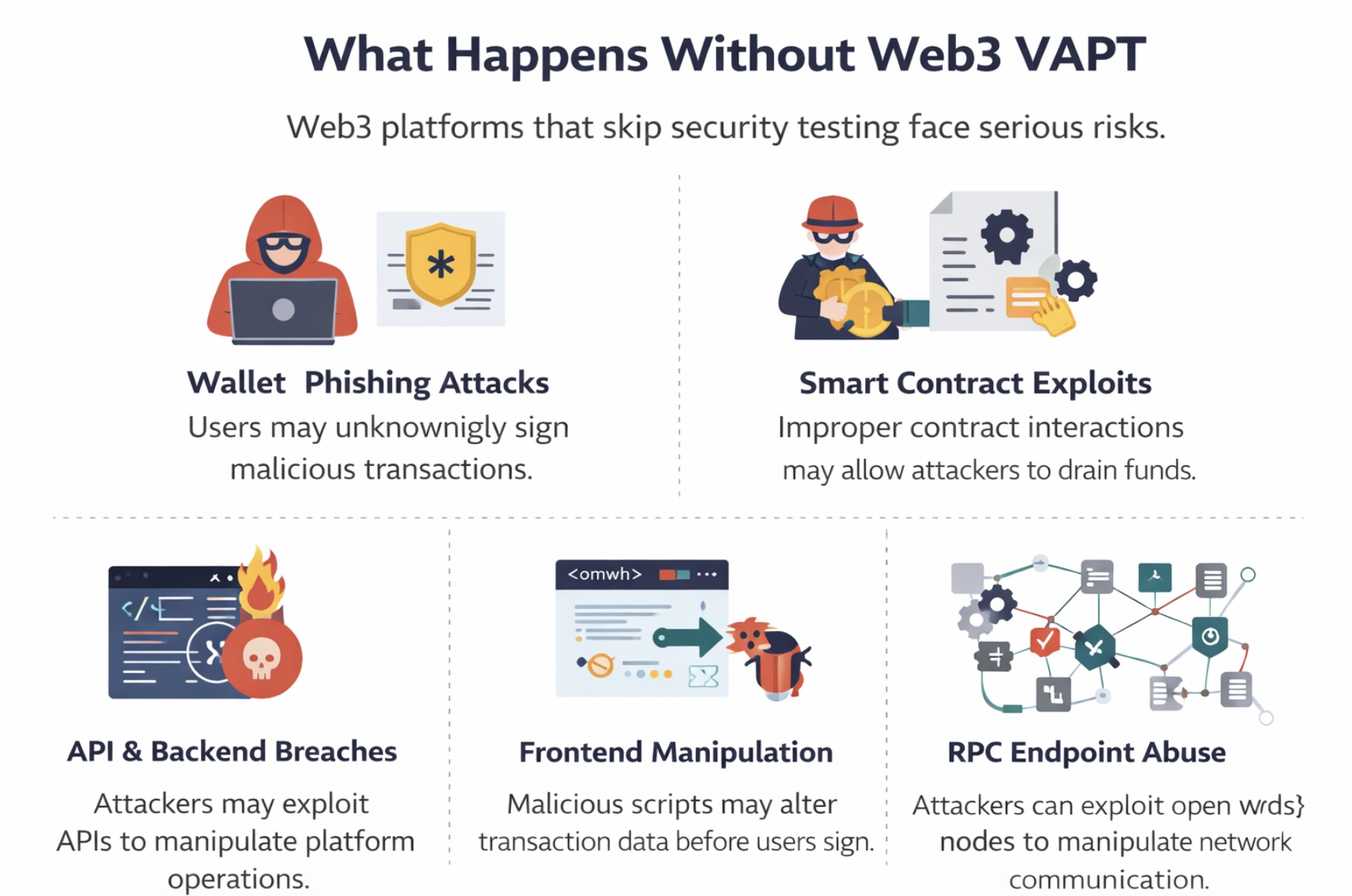
Web3 platforms combine smart contracts, decentralized infrastructure, APIs, wallets, and frontend applications, creating a complex environment where vulnerabilities can exist across multiple layers.
The Web3 VAPT service by i6 Security Solutions provides a comprehensive security assessment of decentralized applications (dApps), blockchain integrations, APIs, and Web3 infrastructure to identify vulnerabilities before attackers exploit them.
Our experts simulate real-world attack scenarios against Web3 platforms, helping organizations secure their applications, protect user assets, and maintain trust within decentralized ecosystems.
Unlike traditional applications, Web3 platforms operate in public blockchain environments where attackers constantly scan for vulnerabilities.
Web3 VAPT ensures your platform is secure across the entire user journey from interface to blockchain execution.
Our Web3 VAPT service evaluates the complete decentralized application ecosystem.
The frontend interface interacts directly with user wallets and blockchain transactions.
Vulnerabilities may exist in how the frontend interacts with contracts.
Wallet connections introduce critical security risks.
APIs and middleware support blockchain interactions.
dApps rely on nodes and RPC endpoints to interact with networks.
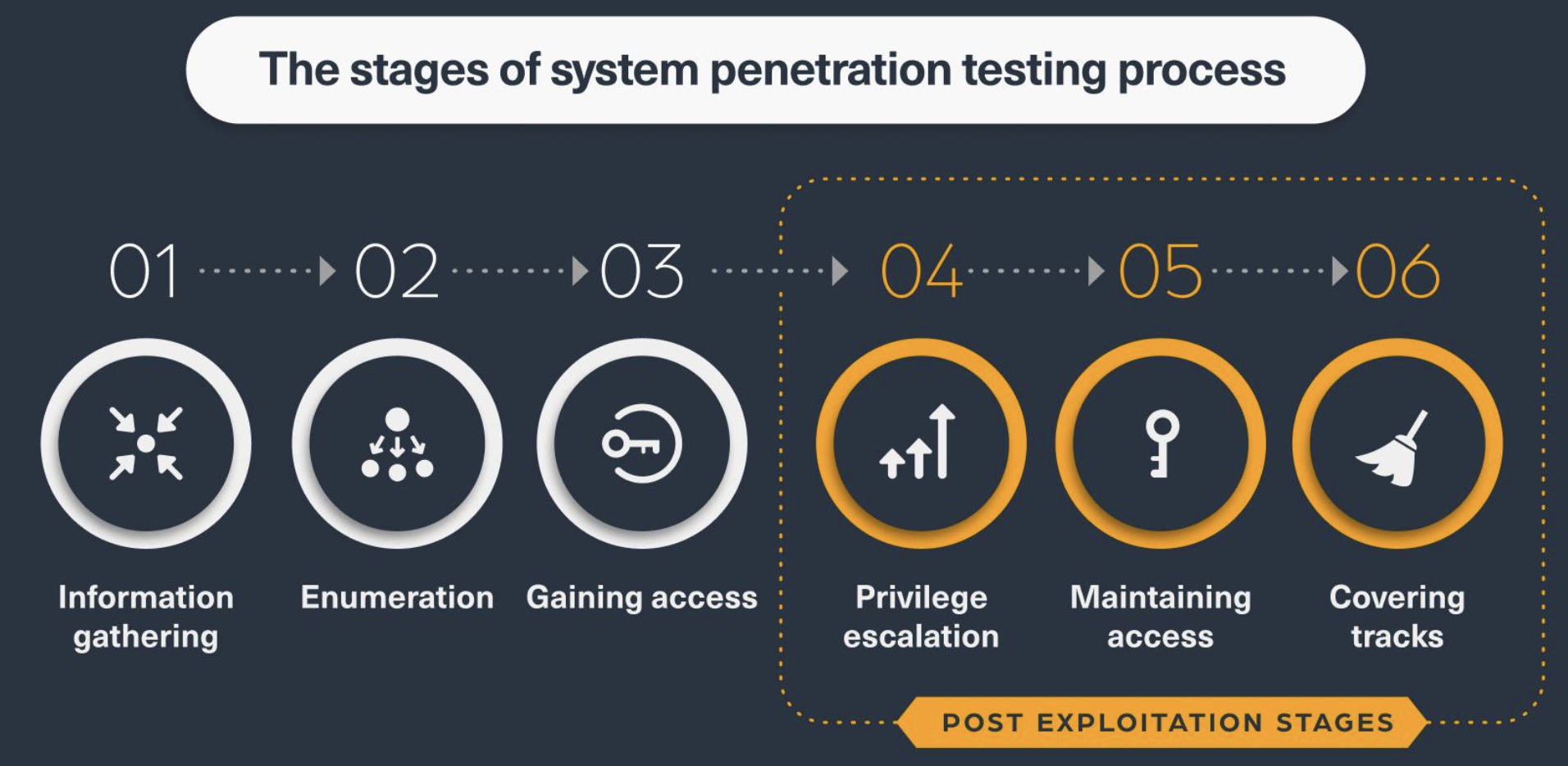
| Phase | Activity | Objective |
|---|---|---|
| Phase 1 | Scope & Architecture Review | Understand dApp architecture and blockchain interactions |
| Phase 2 | Automated Vulnerability Scanning | Identify common security weaknesses |
| Phase 3 | Manual Penetration Testing | Simulate real-world Web3 attack techniques |
| Phase 4 | Smart Contract Interaction Testing | Analyze frontend-contract transaction flows |
| Phase 5 | Wallet & API Security Testing | Identify authentication and integration vulnerabilities |
| Phase 6 | Remiation Guidance | Provide recommendations to fix security issues |
| Framework | Purpose |
|---|---|
| OWASP Top 10 | Web application security risks |
| OWASP Smart Contract Top 10 | Blockchain-specific vulnerabilities |
| OWASP ASVS | Secure application architecture |
| NIST Cybersecurity Framework | Risk-based security controls |
| MITRE ATT&CK Framework | Adversarial attack simulation |
In decentralized ecosystems, security vulnerabilities can lead to immediate financial loss and reputational damage.
i6 Security Solutions helps Web3 innovators secure their platforms through advanced Web3 penetration testing and vulnerability assessments.

Isix is a modern cybersecurity company dedicated to protecting businesses from digital threats. With expert solutions, 24/7 monitoring, and proven strategies, we secure your future in a connected world.