- Home
- Web3 24×7 SOC Monitoring
Web3 24×7 SOC Monitoring
Web3 24×7 SOC Monitoring
Continuous Threat Detection for Blockchain, DeFi, and Web3 Infrastructure
Web3 platforms operate in public, permissionless environments where attackers constantly monitor protocols, smart contracts, wallets, and blockchain infrastructure for exploitable weaknesses. Unlike traditional IT systems, Web3 attacks can occur within seconds and often result in irreversible financial loss.
The Web3 24×7 SOC Monitoring Service by i6 Security Solutions provides specialized monitoring designed for decentralized ecosystems, including smart contracts, blockchain nodes, wallets, APIs, and decentralized applications (dApps).
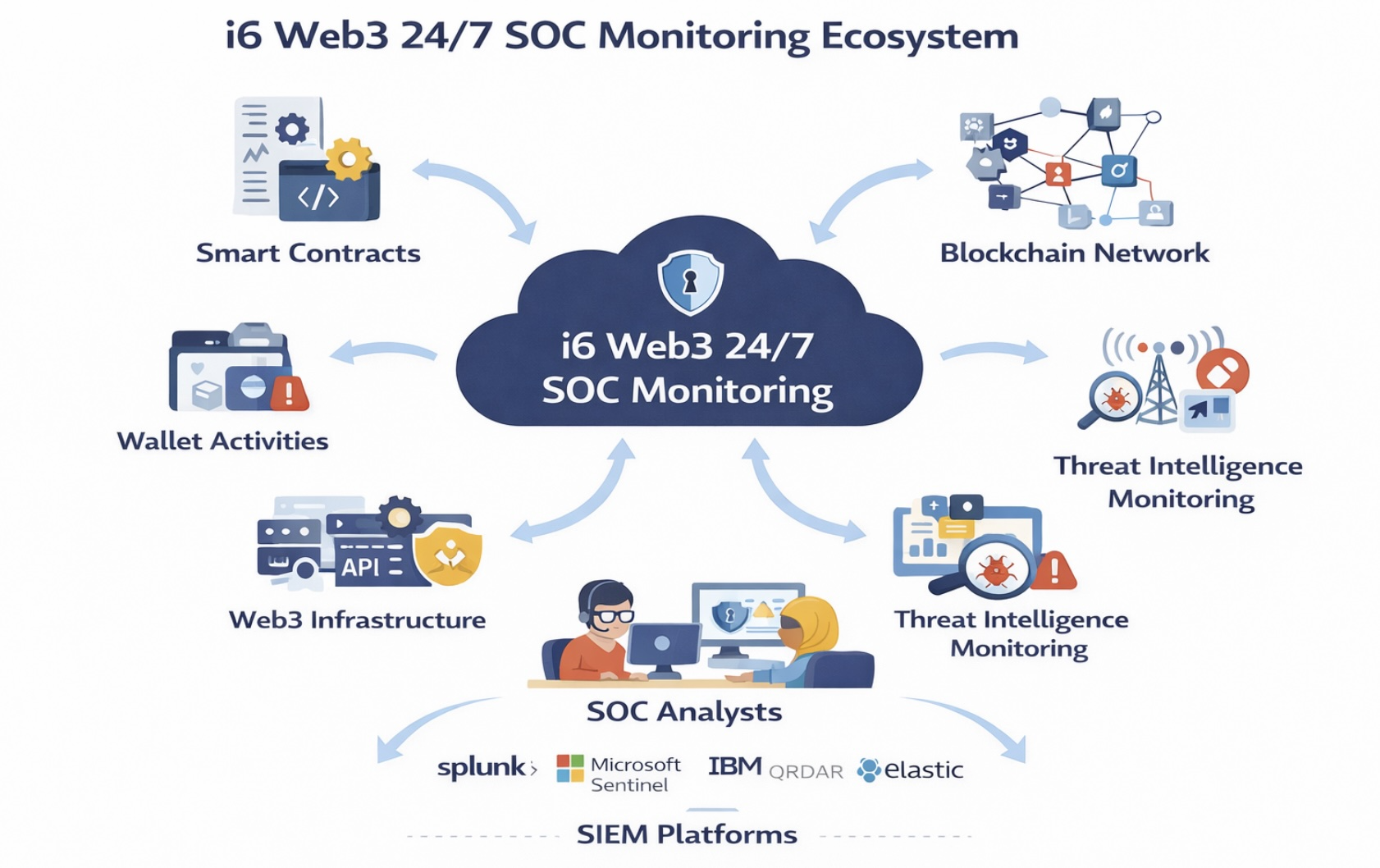
Our SOC continuously analyzes on-chain activities, infrastructure telemetry, security alerts, and threat intelligence to detect suspicious activities and respond before attacks escalate.
The Problem: Lack of Web3 Detection
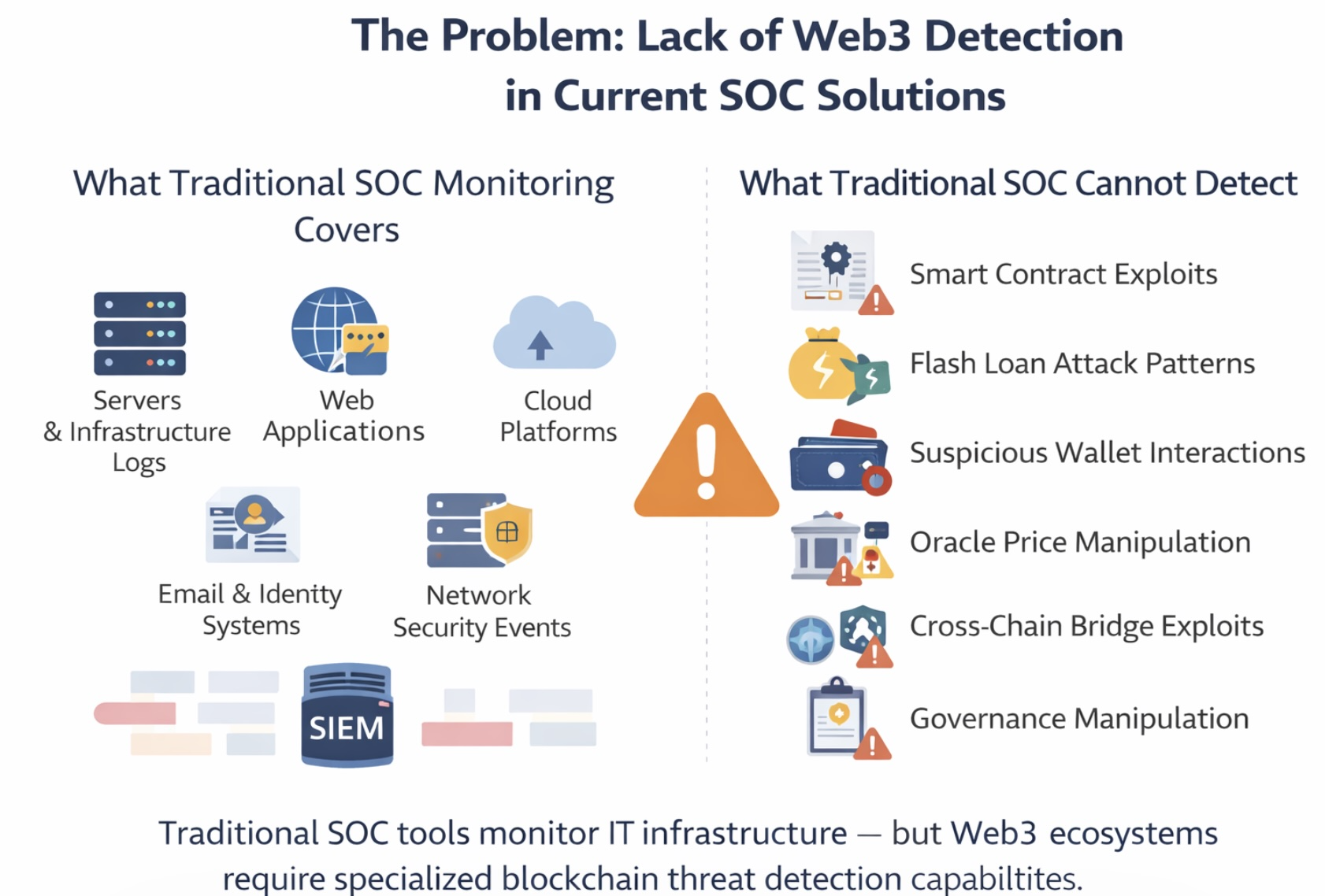
Most enterprise SOC environments rely on traditional SIEM platforms designed for IT networks, applications, and cloud infrastructure. While powerful, they were not originally built to detect Web3-specific attack patterns.
Leading SIEM platforms used globally include: Splunk Enterprise Security, Microsoft Sentinel, IBM QRadar, Google Chronicle, Elastic Security, and LogRhythm.
These platforms lack native detection use cases for blockchain transactions, smart contract interactions, DeFi exploits, and wallet-based attacks. Many Web3 organizations deploy SOC platforms but remain blind to blockchain-specific threats.
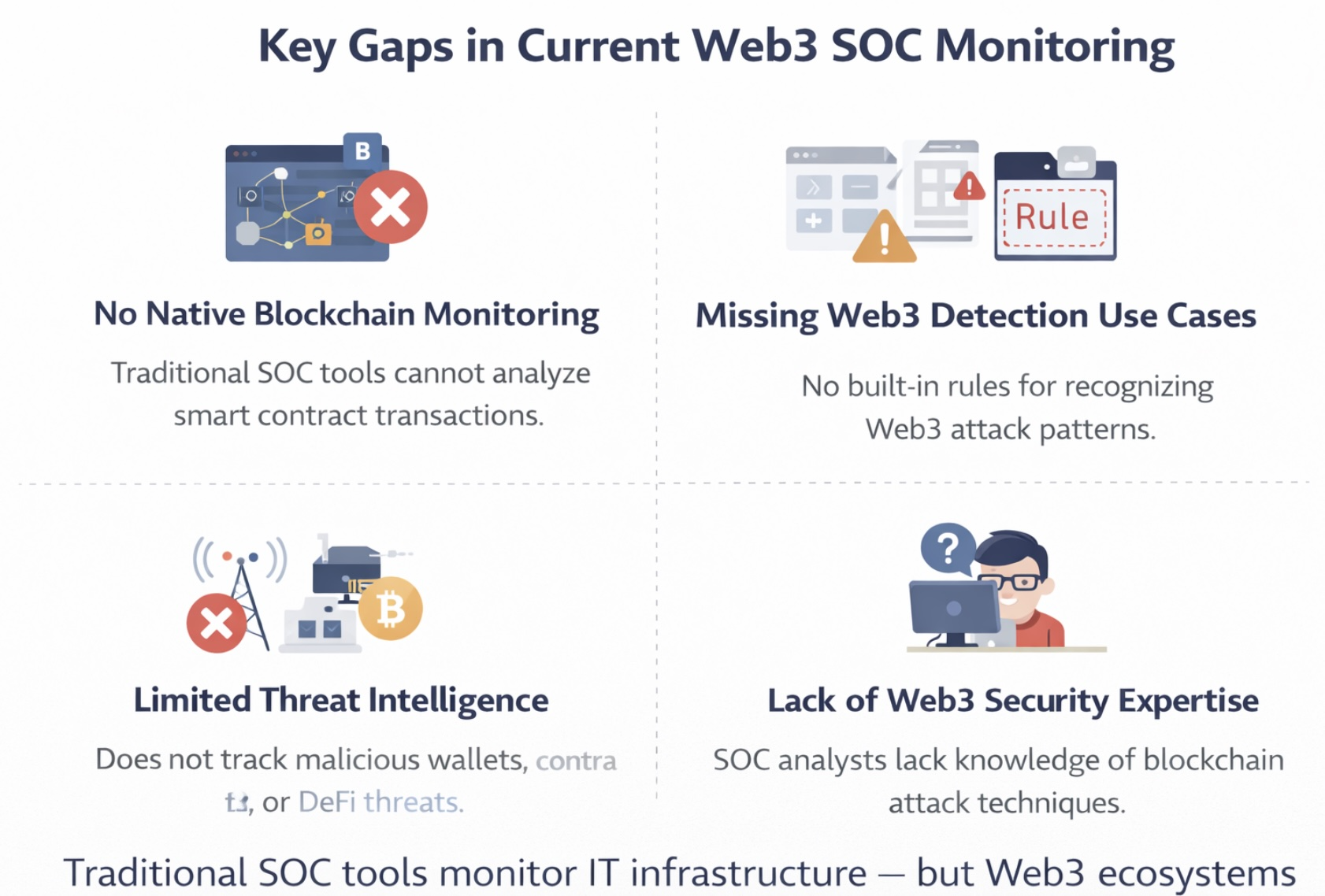
Key Gaps in Current Web3 SOC Monitoring
No Native Blockchain Monitoring
Traditional SOC tools cannot analyze smart contract transactions or on-chain activity patterns.
Missing Web3 Detection Use Cases
Security platforms lack built-in rules for detecting flash loan signals, abnormal contract interactions, and malicious wallet clusters.
Limited Threat Intelligence
Most SOCs lack intel on crypto hacker wallets, malicious DeFi contracts, or blockchain exploit indicators.
Lack of Web3 Security Expertise
Organizations often lack analysts trained to interpret blockchain attack patterns and decentralized infrastructure risks.
i6 Web3 Security Research Labs
To address industry gaps, i6 Security Solutions established dedicated Web3 Security Research Labs to simulate real-world attack scenarios and build detection capabilities for:
- DeFi protocols & smart contract platforms
- Wallet integrations & blockchain nodes
- Decentralized exchanges & cross-chain bridges
Web3 Detection Use Cases Developed by i6
On-Chain Monitoring
- Smart Contract Exploitation Indicators
- Flash Loan Attack Signals
- Suspicious Wallet Activity
Protocol Integrity
- Governance Manipulation Attempts
- Oracle Manipulation Patterns
- Cross-Chain Exploit Signals
Testing Across Leading SIEM Platforms
Our detection logic is pre-tested and integrates with Splunk, Microsoft Sentinel, IBM QRadar, Elastic Security, and Google Chronicle without requiring major architectural changes.
1-Month Free Proof of Concept (POC)
Validate the value of Web3 SOC monitoring before full deployment. We integrate your infrastructure, deploy detection cases, and simulate attacks to provide real insights.

