In a world where 2,000 attacks happen every week, Web 3.0 security is your foundation, not an option. We provide proactive auditing and deep forensic insights for the decentralized frontier.
The Gold Standard in DeFi Protocol Security. — i6 Security Solutions safeguards your smart contracts, tokenomics, and protocol logic through advanced audits, real-world exploit simulations, and expert manual reviews, helping you prevent vulnerabilities, protect user funds, and earn investor trust with an i6 Verified security seal. From deep technical analysis and automated scanning to line-by-line code review, remediation support, and transparent reporting, we deliver a complete DeFi security audit package that strengthens economic resilience, eliminates critical risks, and ensures your platform launches with confidence and zero-loss ambition.
Includes: Line-by-line code review, remediation support, and economic resilience testing.
Request an AuditFull-Stack Security from Interface to Chain. i6 Security Solutions protects your entire Web3 ecosystem by auditing your frontend, APIs, wallet integrations, and smart contracts to prevent UI hijacks, malicious transaction signing, and integration flaws that could expose on-chain assets or compromise user trust. Through comprehensive dApp penetration testing, middleware security reviews, and end-to-end logic verification, we deliver a complete full-stack vulnerability assessment, actionable remediation guidance, and an Integration Security Certificate — ensuring a secure, seamless user journey that drives adoption and long-term retention.
Includes: Penetration testing, middleware reviews, and logic verification.
Request an AuditInstitutional-Grade Audits for High-Volume Infrastructure i6 Security Solutions delivers enterprise-level security assessments for exchanges and crypto platforms, combining Proof of Reserves attestations, wallet architecture protection, and compliance-focused audits to provide the cryptographic transparency, solvency assurance, and operational resilience that regulators, traders, and institutions demand. Through infrastructure stress-testing, wallet and key management reviews, and matching engine security validation, we provide a comprehensive enterprise audit package including a public Proof-of-Reserves report, SOC 2–aligned compliance documentation, and actionable remediation guidance to ensure secure, scalable, and trustworthy trading operations.
Includes: Infrastructure stress-testing and matching engine security validation.
Request an AuditProtecting Provenance and Primary/Secondary Markets. i6 Security Solutions secures your NFT ecosystem end-to-end by auditing minting logic, smart contracts, royalty mechanisms, and metadata storage to prevent mint exploits, enforce creator payouts, and safeguard the authenticity and ownership of every digital asset. Through NFT standard reviews, auction and marketplace logic testing, and decentralized storage verification, we deliver a comprehensive marketplace integrity assessment, actionable remediation guidance, and a Metadata Verification Badge — ensuring transparent trading, fair royalties, and long-term trust across primary and secondary markets.
Request an AuditSecuring the Bedrock of Web3. i6 Security Solutions protects the core of your blockchain by auditing consensus mechanisms, node infrastructure, and peer-to-peer layers to prevent 51% attacks, Sybil threats, eclipse exploits, and network instability while ensuring secure scalability across bridges, rollups, and Layer-2 environments. Through formal protocol verification, node client penetration testing, and end-to-end network resilience assessments, we deliver a comprehensive protocol stability blueprint and a Network Security Attestation for validators — empowering your ecosystem with stronger finality, higher trust, and institutional-grade reliability.
Request an AuditFortifying the Entry Point to Digital Wealthi6 Security Solutions secures next-generation wallets with advanced key management audits, cryptographic validation, and client-side security testing to protect private keys, prevent unauthorized transactions, and safeguard user assets across mobile, web, and extension environments.
Request an AuditWeb3 Gaming & Metaverse Security for High-Value Virtual Economies i6 Security Solutions delivers specialized VAPT for GameFi and metaverse platforms, protecting smart contracts, in-game assets, wallets, APIs, and user accounts from exploits, cheating, asset theft, and economic manipulation to ensure fair play, secure transactions, and uninterrupted gameplay. Through end-to-end penetration testing, smart contract audits, backend and API security validation, and real-world attack simulations, we provide a comprehensive vulnerability assessment, actionable remediation guidance, and a certified security report — empowering your platform with resilient virtual economies, player trust, and scalable, hack-resistant growth.
Request an Audit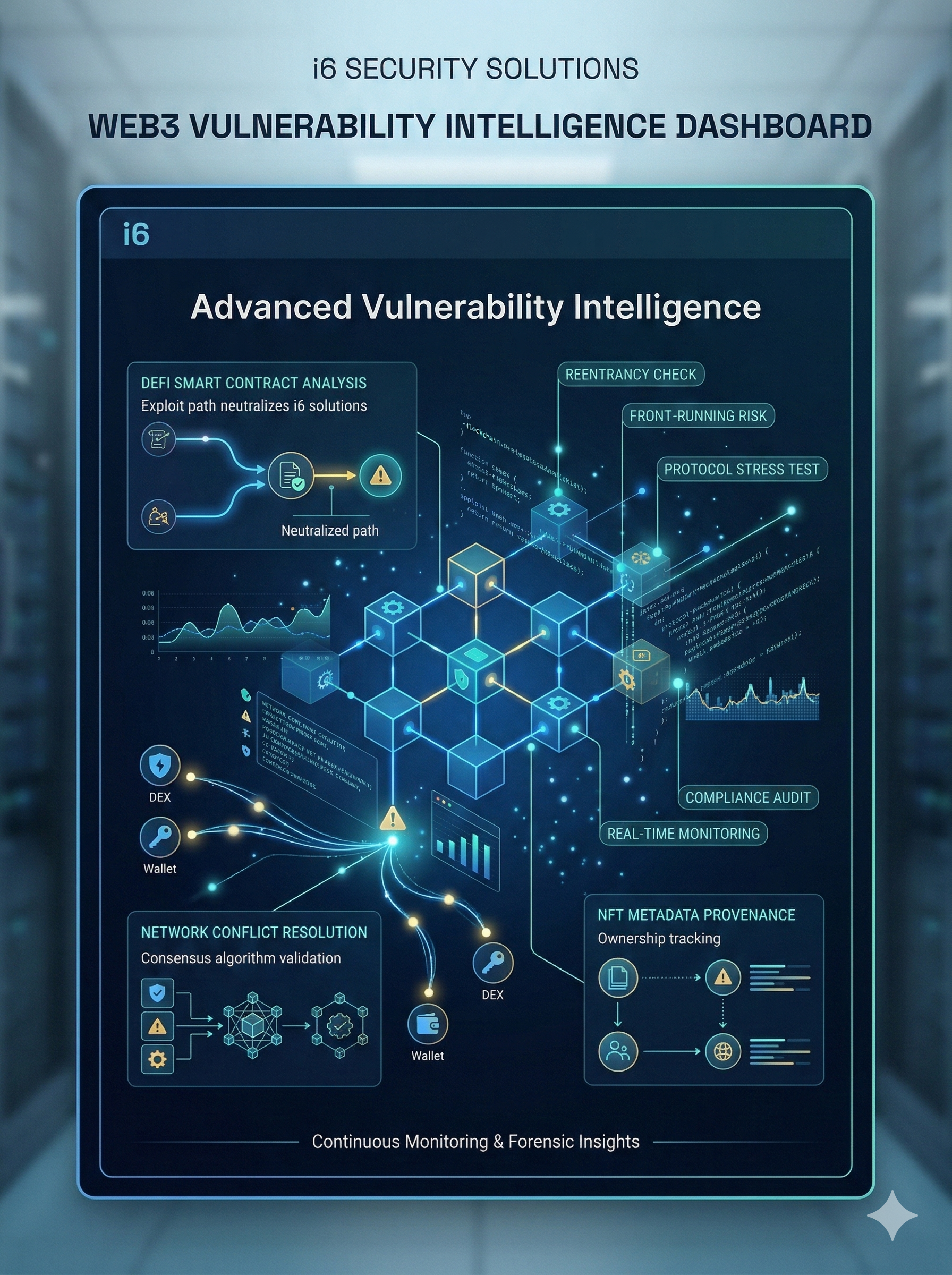
Advanced Vulnerability Intelligence
We leverage a continuously evolving repository of real-world smart contract vulnerabilities and protocol attack scenarios. Our research-driven approach identifies emerging threats before they can be exploited.
Real-world intelligence on exploit patterns and protocol attack scenarios.
Continuous monitoring of emerging vectors in DeFi and Cross-Chain bridges.
Precision tools for auditing code against historical breach patterns.
Deep insights from bug bounty data and security community discoveries.
Auditor community analytics to ensure the highest standards of review.
Security training modules for developers and protocol teams.
Detailed Cyber Security Attacks & Vulnerabilities detected across the Web3 landscape.
Flash loan-driven distortions affecting lending protocols and AMMs.
Validation logic failures in interoperability layers and message passing.
Advanced recursive calls exploiting cross-contract state discrepancies.
Vulnerabilities in voting weight calculations and proposal execution.
Thorough review of contract logic and exploit paths before deployment.
Assessment of blockchain nodes, network config, and server environments.
Evaluation of blockchain mechanics and protocol configuration risks.
Trace malicious transactions and investigate suspicious on-chain activity.
Simulate real-world attacks on dApps and decentralized systems.
Continuous threat hunting tailored for Web 3.0 environments.

Isix is a modern cybersecurity company dedicated to protecting businesses from digital threats. With expert solutions, 24/7 monitoring, and proven strategies, we secure your future in a connected world.